New cybersecurity threats like phishing attacks, ransomware, and scams are always popping up. Stay up to date on the latest widespread threats and protection methods in our recurring series.
MARRIOTT/STARWOOD HOTELS DATA BREACH

Starwood Hotels under Marriott announced that data for as many as 500 million customers was breached, and that it appears someone had unauthorized access to their database since 2014.
The information taken includes guest’s names, postal addresses, phone numbers, birth dates, gender, email addresses, passport numbers, Starwoods reward information, arrival and departure information, reservation dates, and communication preferences. “Starwood said an unknown number of records contained encrypted credit card data, but has ‘not been able to rule out’ that the components needed to decrypt the data wasn’t also taken” (TechCrunch). The company said that only their Starwood brand seems to be affected, as the Marriott hotels booking system is on a separate network.
What to do: Marriott is in the process of sending out emails to affected customers. Breach notifications will only come from “starwoodhotels@email-marriott.com”. It’s popular for hackers to take the information from breaches like this to execute phishing attacks, so do not reply to or click links in notification emails from any other address.
If you’ve been a customer at Starwood in the past four years, keep an eye on your bank statements and accounts for any suspicious activity. Watch in particular for small purchases or withdrawals that you don’t recognize, as that could be a sign of someone testing the account before making a larger withdrawal.
We also recommend changing the password on any accounts that share the same password as the one used on your Marriott/Starwood account.
As part of its response to the breach, Marriott is allowing its customers to sign up free with WebWatcher for one year, which will alert you if your personal information is found on shady websites. You can find out more about this offer and the breach itself here.
USPS CUSTOMER DATA EXPOSED

The United States Postal Service recently fixed this issue that allowed anyone with an account to view the account details for 60 million other users, and even modify their account details. This resulted from an authentication weakness in the USPS’s Informed Visibility service. It was designed to provide businesses, advertisers, and other high-volume senders with near real-time tracking data. The flaw let any logged-in user “query the system for account details belonging to any other users, such as email address, username, user ID, account number, street address, phone number, authorized users, mailing campaign data and other information” (Krebs On Security).
Luckily the USPS seems to have fixed the vulnerability and put greater access controls into place.
What to do: It doesn’t appear that customer information or login credentials were exposed, so hopefully there are no negative effects from this error. If you have a USPS account, ensure that none of your account information has been changed, and change your password if you want to take extra precautions.
HSBC DATA BREACH

The international banking institution HSBC alerted some of its customers earlier this month that their account information had been compromised. According to the bank, less than 1% of its customers were affected. Information accessed includes customer names, mailing addresses, phone numbers, email addresses, dates of birth, account numbers, account types, account balances, transaction histories, statement histories, and possibly even more data.
What to do: Affected customers should have received a notification from HSBC. They recommend changing your password and placing a fraud alert on your account. They are also offering a one-year subscription to Identity Guard credit monitoring service. Even if you did not receive a notification that your data was breached, it’s still smart to update your password and look out for unusual activity if you are an HSBC customer.
GAMES ON GOOGLE PLAY STORE INSTALLING MALWARE
13 driving-themed games were recently taken down from the Google Play Store after it was discovered they were installing malware on users’ phones. The malicious apps were downloaded more than 560,000 times before being removed, and all came from a developer called Luiz O Pinto. Once the app was downloaded, it would download an additional file called “Game Center” and require the user to install it. The malware would hide from view and then proceed to display ads when the device was unlocked.
Here is a list of the apps in question:
- “Truck Cargo Simulator”
- “Extreme Car Driving Racing”
- “City Traffic Moto Racing”
- “Moto Cross Extreme Racing”
- “Hyper Car Driving Simulator”
- “Extreme Car Driving City”
- “Firefighter — Fire Truck Simulator”
- “Car Driving Simulator”
- “Extreme Sport Car Driving”
- “SUV 4×4 Driving Simulator”
- “Luxury Car Parking”
- “Luxury Cars SUV Traffic”
- “SUV City Climb Parking”
What to do: If you downloaded any of these apps, uninstall them immediately! Then run an antivirus and anti-malware scan on your phone to ensure any infections are removed.
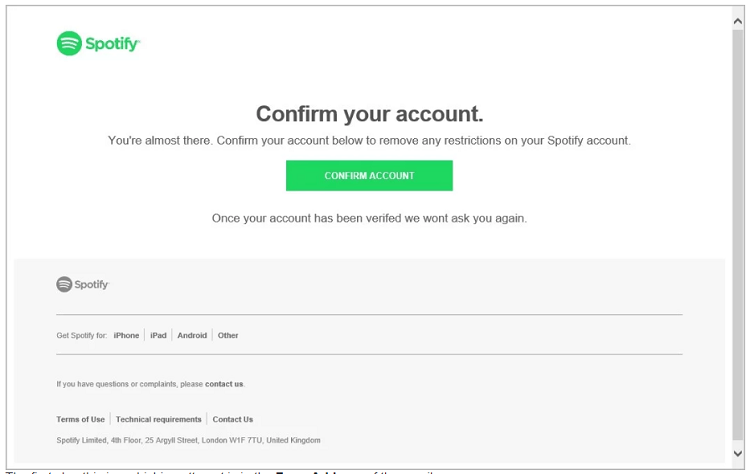
SPOTIFY PHISHING CAMPAIGN
Some users are receiving phony emails that lure the recipient to click on a link to confirm their Spotify account and remove any account restrictions. The link leads to a fake Spotify login page that will steal login credentials if entered.
What to do: Luckily there are many giveaways in the email and fake login page. The “from” address in the email line is clearly not from Spotify, and the webpage’s URL is not Spotify.com. Take a moment to review emails like this and watch out for the telltale warning signs of an attack.
![]() If you need some extra help identifying or protecting against any of these or other cybersecurity threats, let us know!
If you need some extra help identifying or protecting against any of these or other cybersecurity threats, let us know!