Technology & Business Guides
Tips, tools, and information about all things IT and business.
Business Technology & Managed IT Service
Signs You Should Switch Managed IT Providers (And How to Make it Painless)
No relationship is perfect, and the same goes for business relationships. Sometimes you just need to know when enough is enough and it’s time to cut ties with your managed IT service provider.

How a Managed Service Provider Protects Your Company
Learn all about managed service providers and how they can help your business stay secure, productive, and successful.

Switching From Traditional IT Support to Managed Services
Learn about the differences between traditional and managed IT support, and how to make your transition to managed IT easier if you’re ready to take the leap.

Outsourcing Isn't a Bad Word
Many businesses don’t have access to the IT help they need to truly thrive. Outsourced assistance can make all the difference.

The Modern Lawyer's Technology Guide
The tips every law office needs to stay secure, productive, and successful in today’s modern business world.
What is a Managed Services Provider?
Technology helps manage business. But it’s often difficult and expensive for a business to effectively manage its technology. This is where a managed service provider can help. Learn how in our guide.
The Business Owner's Guide to Modern IT Management
How to keep your business safe, productive, and successful in today’s world by taking advantage of new technology and managed support.

The Ultimate Guide to Business Technology
Wondering what technology your business could benefit from? Learn what’s out there and what’s right for you.

The Ultimate Guide to Managed IT Services
Learn all about managed IT – how it started and why, what managed service providers do, and who they’re a fit for.
Security

How to Protect and Control Your Online Identity
Simple ways to protect yourself from identity theft, online scams, and stolen data and control your public information.

The Ultimate Guide to Phishing Scams for SMBs
Learn about the common phishing scams targeting businesses, and how to avoid becoming a victim.
How to Create (and Remember!) Strong Passwords
It’s time to rethink the way you create passwords! Learn methods to make secure passwords that you can actually remember.
The 10 Commandments of Computer Security
Follow our tips to be sure you’re protected against cyber attacks, theft, and data loss.

5 Steps to Protect Your Law Firm's Private Data
Law firms have invaluable client, case, and financial files to protect. Keep your precious data safe from hackers, human error, and hardware failure.

The Ultimate Guide to Phishing Scams for SMBs
An expanded, web-based version of our downloadable guide. Learn about all the common threats SMBs face, and how to avoid becoming a victim.
Backup, Disaster Recovery, & Business Continuity
Life After Quarantine
The business world has changed drastically due to COVID. As companies look to re-open and return to regular office life, how can you keep both your employees and operations safe and productive? Check out our guidelines in this eBook.
The Quick Guide to Backup & Disaster Recovery
Backup and disaster recovery can seem overwhelming. In this guide, we make it straightforward and easy to understand. Learn about how they can help your business, and how to find the right solution.
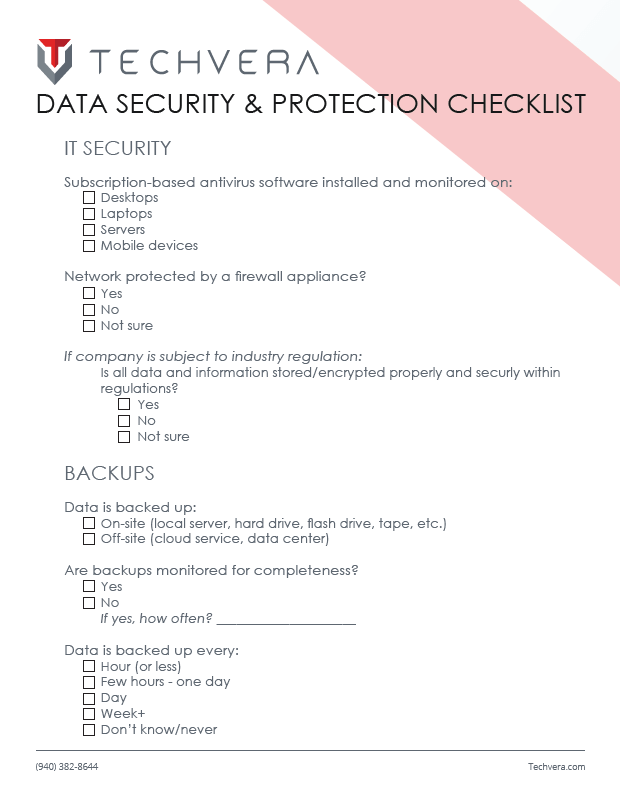
Data Security & Protection Checklist
Use our checklist to keep track of your business’ backup, security, and disaster recovery procedures and readiness.
Cloud Technology, Mobility, & Productivity
Automating Business Processes
Learn how to take advantage of AI, machine learning, and automation technology to save time + revenue, and get more done!
The Quick Guide to VoIP
Voice over IP (VoIP) technology offers way more than just phone service! Learn how VoIP works, and the benefits it can bring to your business.

The Quick Guide to Cloud Services for Business
The cloud is a great tool for your business’ security, productivity, and mobility. Learn how to take advantage of this technology!
Miscellaneous
Buyer Persona Workbook
Having trouble finding your perfect clients? Use our fillable workbook to easily create your ideal customer personas.
HIPAA Compliance Guide
An overview of the Health Insurance Portability and Accountability Act (HIPAA) compliance requirements. It covers the relevant legislation, required procedures, and ways that your business can achieve compliance.